How to Evaluate a Cyber Security Expert’s Portfolio Before Hiring
- 1 min read
Learn how to assess a cyber security expert’s portfolio with a structured, risk-focused approach before hiring.

Why Hiring the Wrong Cyber Security Expert Is a Strategic Risk
Cyber security hiring is not a routine recruitment decision. It is a risk management decision.
In Europe’s regulatory environment, security failures carry financial penalties, reputational damage, and operational disruption. From GDPR enforcement to sector-specific compliance, the margin for error is shrinking.
Many organizations review resumes. Few properly analyze portfolios.
A cyber security expert’s portfolio reveals execution capability, regulatory understanding, and architectural depth. For enterprise IT leaders, structured evaluation is essential.
The Challenge - Portfolios That Look Impressive but Lack Depth
Security portfolios often include:
- Certifications
- Tool lists
- General project descriptions
- High-level claims
However, these elements alone do not demonstrate strategic capability.
According to research from Gartner, security maturity depends more on implementation discipline than on tool adoption.
Your evaluation process must go deeper.
Step 1 - Assess Alignment with Recognized Frameworks


A credible portfolio should reference structured frameworks, not isolated activities.
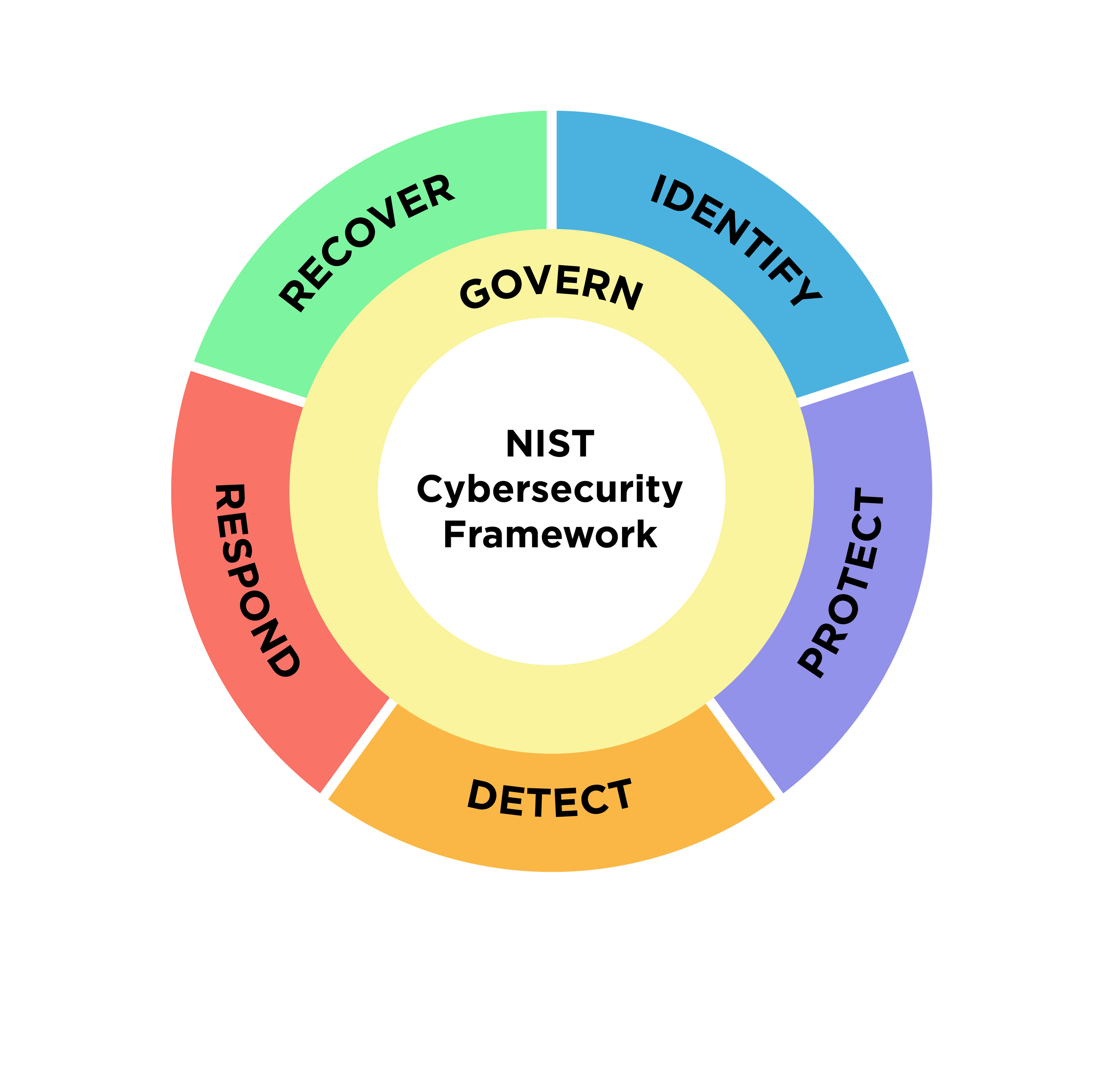
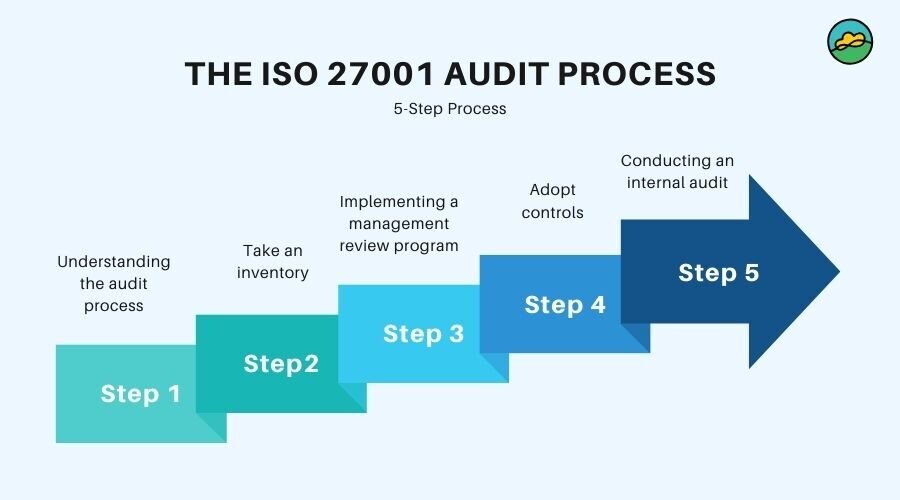
Look for alignment with:
- National Institute of Standards and Technology Cybersecurity Framework
- International Organization for Standardization ISO 27001
- EU data protection regulations
- Industry-specific compliance standards
Red flag: If the portfolio focuses only on penetration testing without governance context.
Strong candidates demonstrate:
- Risk identification methodology
- Control mapping
- Gap analysis documentation
- Continuous improvement cycles
Framework literacy indicates enterprise readiness.
Step 2 - Examine Real-World Project Depth
Surface-level case studies are insufficient.
Ask for clarity on:
- Industry vertical
- Organizational size
- Security maturity level at project start
- Specific risks addressed
- Measurable outcomes
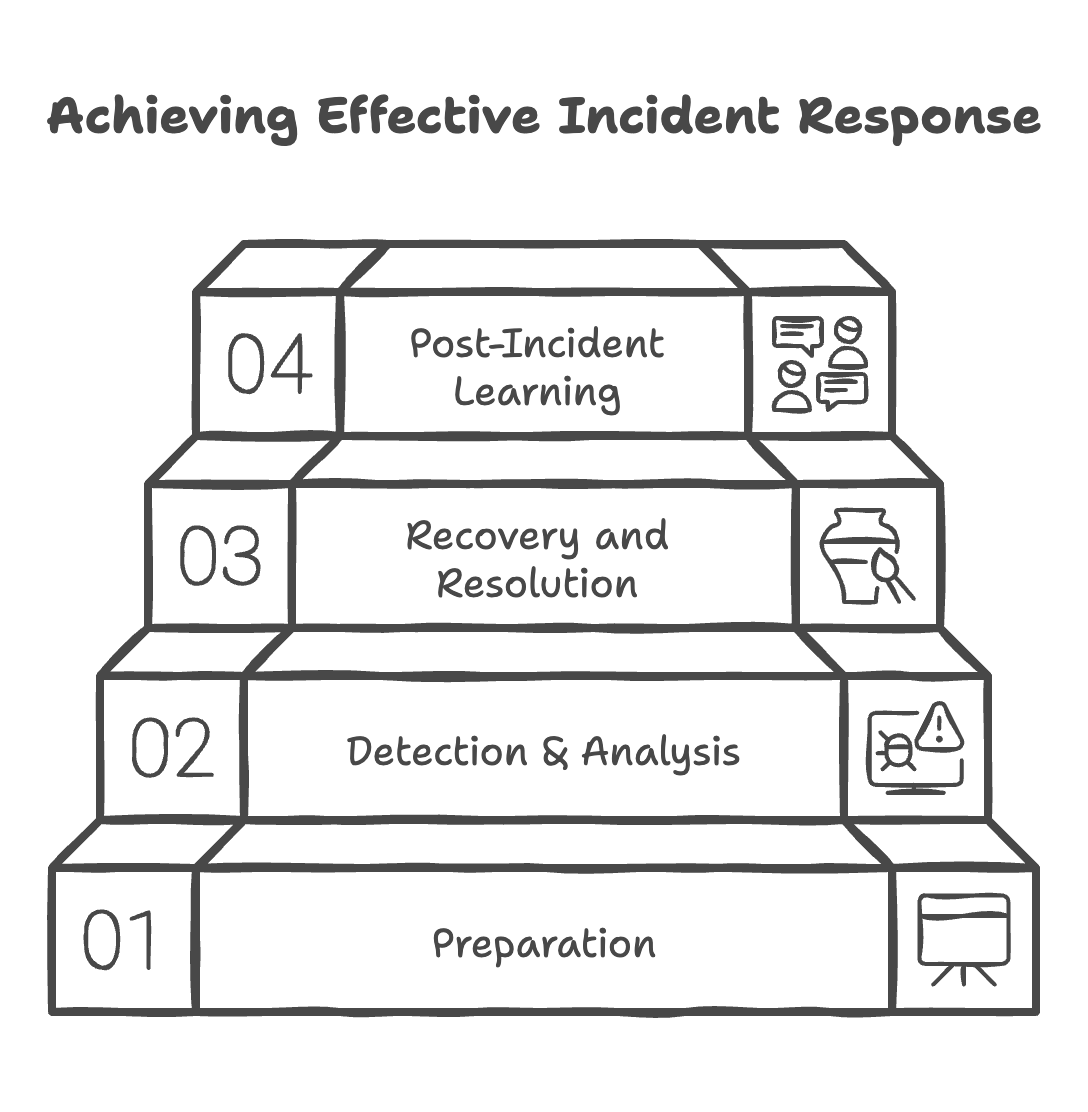
Did the expert reduce incident response time? Did they improve audit readiness? Did they restructure access governance?
Reports from McKinsey & Company emphasize that measurable security transformation requires both technical and organizational change.
Portfolios should reflect both dimensions.
Step 3 - Evaluate Technical Breadth and Integration Capability
Modern enterprise security is not siloed.
An effective cyber security expert understands:
- Cloud security architecture
- Identity and access management
- DevSecOps integration
- Endpoint and network protection
- Incident response automation
The portfolio should show integration across systems, not tool configuration in isolation.
For example:
- Integration of SIEM with cloud infrastructure
- Automated compliance monitoring
- Secure SDLC implementation
Technical architecture diagrams and workflow documentation are strong indicators of competence.
Step 4 - Analyze Risk Management Thinking
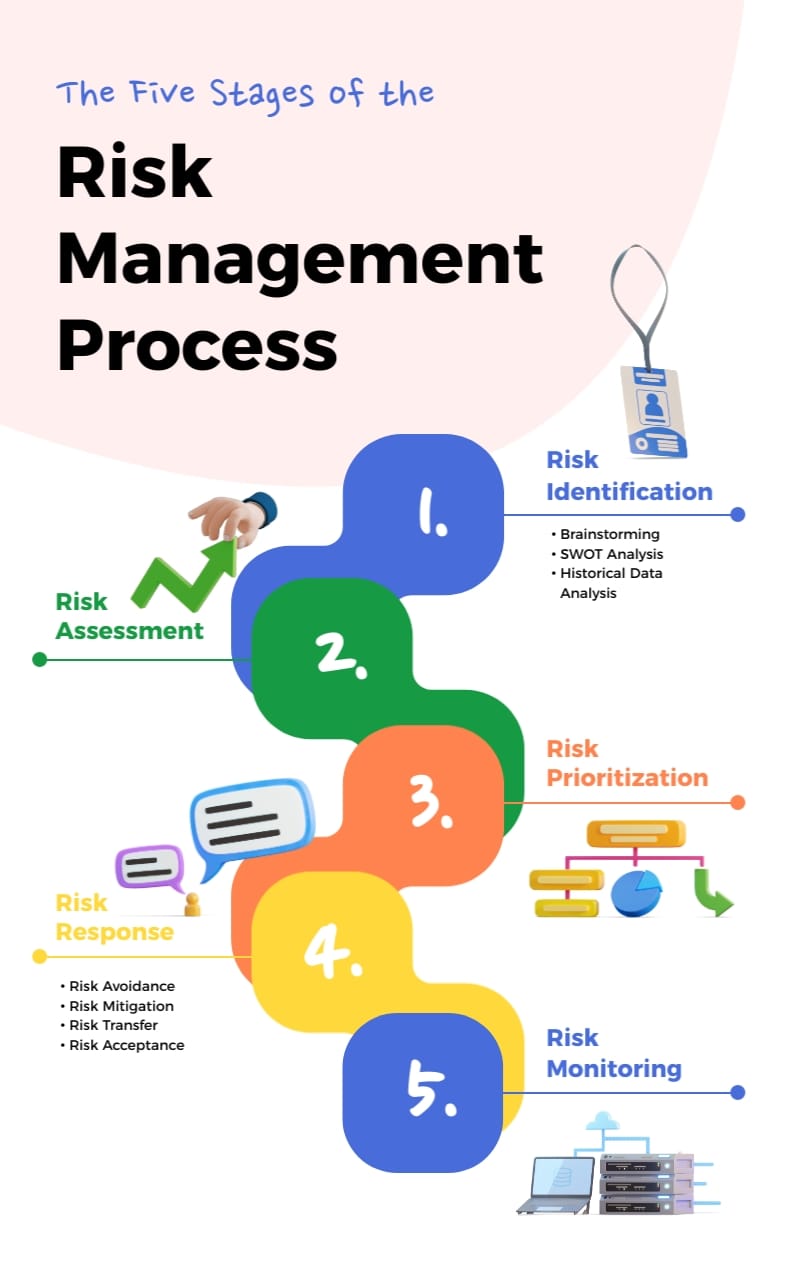


Security expertise is ultimately about risk prioritization.
A mature portfolio demonstrates:
- Risk scoring methodologies
- Threat modeling exercises
- Business impact analysis
- Executive reporting capability
Guidance from European Union Agency for Cybersecurity highlights the importance of structured risk assessment in European enterprises.
If a candidate cannot clearly articulate how they prioritize risk, strategic decision-making may be weak.
Step 5 - Review Communication and Documentation Quality
Security professionals must communicate with:
- CIOs
- CTOs
- Compliance officers
- Non-technical executives
Evaluate the clarity of their documentation.
Strong indicators include:
- Executive summaries
- Structured audit reports
- Actionable remediation roadmaps
- Clearly defined KPIs
A technically strong expert who cannot translate risk into business language may limit organizational adoption.
Industry Insight
Enterprise cyber security spending continues to increase across Europe.
According to Gartner, global information security spending is projected to grow steadily year over year, driven by cloud adoption and regulatory pressure.
Meanwhile, research from McKinsey & Company suggests that organizations integrating security into digital transformation initiatives achieve stronger resilience outcomes than those treating it as a standalone function.
The implication is clear. Portfolio evaluation must focus on strategic integration, not isolated credentials.
Euro IT Sourcing Perspective
From our experience working with European technology-driven organizations, the strongest cyber security professionals share common traits:
- They document processes rigorously.
- They connect technical controls to business risk.
- They understand EU regulatory context.
- They collaborate effectively with DevOps and infrastructure teams.
We consistently observe that security projects succeed when experts combine governance knowledge with hands-on technical capability.
Portfolio review should test for both.
Results and Business Impact
A properly evaluated and strategically aligned cyber security hire can deliver:
- Reduced incident response time by 30-50 percent
- Improved audit success rates
- Lower regulatory exposure within EU jurisdictions
- Stronger cloud security posture
- Enhanced stakeholder confidence
Poor hiring decisions, in contrast, often result in fragmented tools, inconsistent documentation, and increased operational risk.
The portfolio review phase directly influences these outcomes.
Key Takeaways
- Evaluate framework alignment before technical tools.
- Demand measurable project outcomes.
- Prioritize risk management thinking over certifications alone.
- Assess integration capability across enterprise systems.
- Review documentation quality as carefully as technical skills.
Author & Contact
Author: Matt Borekci https://www.linkedin.com/in/matt-borekci
Contact Us: https://www.euroitsourcing.com/en/contact

Turkish Tech Renaissance: The Remarkable Growth of the IT Industry
Turkey's IT industry is rapidly growing, driven by its strategic geographic location, a young and educated workforce, and strong government support. The country's thriving startup ecosystem, emphasis on digital transformation, and increasing IT exports are positioning Turkey as a significant player in the global technology landscape. This growth trajectory highlights Turkey's potential and ambition in shaping the future of technology both domestically and internationally.

TURKIYE: The Rising Star of IT Outsourcing
Turkey is quickly becoming a key player in the IT outsourcing industry, thanks to its strategic location, skilled workforce, and cost-effective solutions. Positioned between Europe and Asia, Turkey offers businesses access to top-tier IT talent at competitive prices, with minimal language and cultural barriers. The country's commitment to data protection and innovation further enhances its appeal as a reliable and cutting-edge IT outsourcing partner.